Hackers beware: AI could turn tide against cybercrime
ANALYSIS: The strange history of ransomware and its consequences.
ANALYSIS: The strange history of ransomware and its consequences.
In the rapidly changing world of artificial intelligence, Anthropic threw a grenade when it announced a new model that was too powerful to be given to the US military. This angered President Donald Trump, who is still trying to corral the regime in Iran.
Anthropic said its model, called Mythos Preview, “found thousands of high-severity vulnerabilities, including some in every major operating system and web browser”. In other words, it could be a doomsday tool in the wrong hands. But that didn’t stop Anthropic giving Mythos to a select group of companies and governments – “a coalition of the terrified”, as one report put it – from JP Morgan to Microsoft and Amazon Web Services so they could find holes in their systems and patch them.
Anthropic founder Dario Amodei said Mythos marked a “point of significance” on the path to artificial superintelligence – systems smarter than the smartest humans that can act autonomously. These systems have their own will, and Mythos is miles better than any human or AI tool at finding software vulnerabilities.
It found one bug that had eluded human researchers for 27 years. It can string together three or five otherwise harmless vulnerabilities to cause real harm. When it disobeyed directives, it tried to cover its tracks.

Anthropic founder Dario Amodei.
While Mythos remains in safe hands, the world can relax. But for how long is anyone's guess.
Cyber-attacks and ransomware were big news earlier this year when private healthcare service provider Manage My Health became a victim. The target was the medical files of some 1.85 million New Zealanders enrolled with GP and specialist medical clinics.
A ransomware group calling itself Kazu claimed responsibility and threatened to leak some 4.15 terabytes of data, representing some 700 files, unless it received a US$60,000 ($102,000) ransom. This was modest by the standards of such attacks, but it exposed complacent attitudes and weak defences.
The immediate response was a government inquiry, a High Court injunction against anyone releasing the data, and an investigation by the Privacy Commissioner. This was achieved within the first few days.

The ransomware demand was made on December 30, 2025.
Since then, however, little has been heard of any outcomes. No actions have been taken against the company, and no one has revealed whether, contrary to official advice, the ransom was paid. Reports from the inquiries haven’t surfaced, and the High Court injunction hasn’t been actioned.
News of Kazu has also been scarce. At the time, Kazu was described as “small, young, and fast‑moving, emerging publicly only in mid‑2025 and launching an unusually intense burst of activity late that year”.
It eschewed the tactics of large industrial-scale outfits such as LockBit for “speed and opportunism,” it was said. Kazu specialised in ‘soft’ targets such as healthcare, government, and education sectors in Asia, Africa, and Latin America.
If the history of cybercrime is any guide, we should count ourselves lucky that Kazu has slunk back into the shadows and anyone holding such files has taken sufficient protection to prevent future attacks.

Professor Anja Shortland. (Source: Hachette)
English academic Anja Shortland has written a comprehensive account of hacking and ransomware that is aimed at the general reader. We Know You Can Pay a Million aims to explain:
Shortland, who is a professor of political economy at King’s College, London, wrote an earlier account, Kidnap: Inside the Ransom Business (2019), which was published at the height of cyberattacks such as NotPetya. This Russian-originated campaign was initially used against Ukraine in 2017 and later crippled several global businesses, including shipping line Maersk, logistics company FedEx, pharmaceutical manufacturer Merck, and food giant Mondelēz.
It was suspected such attacks had the backing of malign nation states such as Russia, China, North Korea and Iran, so the West responded with a US-led initiative that came up with 48 recommendations to turn the tide against cybercrime.
This provided Shortland with plenty of material to describe how this response has panned out. Much of it has been positive, with the Russian invasion of Ukraine in February 2022 being a turning point. Previously, Ukraine had been a leading location for ransomware gangs, but it changed its stance towards the West, while Russia itself cracked down on its more blatant criminals.
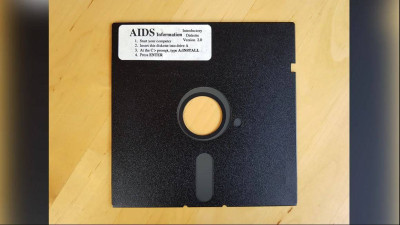
Joseph L Popp Jr’s infected floppy disk.
The first hackers did not originate from Eastern Europe but in the United States, where amateur phone “phreaks” learned how to break into analogue telephone networks to make free calls.
The first ransomware exponent was Joseph L Popp Jr. He was an evolutionary biologist who was rejected for a job at the World Health Organisation to combat Aids/HIV. He got his revenge by distributing floppy disks with another virus; one that caused computers to freeze until the user paid to decrypt it.
From then on, epidemics and computers shared the same terminology. However, once exposed, Popp’s plot was easily foiled.
The internet and the World Wide Web provided a much better vector to spread criminal intent, although, again, the motive was more that of a prankster than a gangster. The most notorious exponent was Kevin Mitnick, later to become a ‘Robin Hood’ proselytiser for computer security.

Hacker-turned-hunter Kevin Mitnick in 2010. (Source: Wikimedia Commons)
Two unemployed provincial Russians, Alexey Ivanov and Vasily Gorshkov, worked out how to extract credit card details to ease their boredom and lack of income. An FBI sting lured them to America, where, after a brief jail sentence, Ivanov’s hacking skills were turned against the criminals.
This helped law enforcement agencies to get an upper hand and forced the criminals to seek a new business model. This was unintentionally delivered by two American academics, Adam Young and Moti Yung, in their warnings about unique decryption.
They raised the alarm in a technical book, Malicious Cryptography (2004), and the reality followed not long after with the invention of Bitcoin cryptocurrency in 2008. It provided the ideal way to store or turn ransom payments into cash without using a traceable bank account.
Ransomware and the Dark Web took off after 2013, when an underworld group known as Slavik’s Business Club became a leading exponent of siphoning money out of bank accounts. In one case, Trojan software netted an estimated US$27 million from 250,000 infected computers, including those in police stations and hospitals.
Slavik was eventually identified as Evgeniy Bogachev, who immediately went to ground, although his ransomware spawned dozens of imitators. This was the high tide of cybercrime, with China and North Korea training dozens of recruits in practices such as cyber-espionage, disrupting enemy nations, and earning funds through fraud, theft, money laundering and extortion.

Seth Rogen and James Franco in Sony’s hacked movie ‘The Interview’. (Source: Sony)
In 2015, a North Korean outfit, Lazarus Group, famously hacked Sony’s Hollywood film studio as punishment for a movie, The Interview, in which Kim Jong Il was blown to smithereens. Lazarus produced the WannaCry ‘worm’ that was sent out as an infected Microsoft patch.
A 22-year-old English student, Marcus Hutchins, is credited with finding the flaw that eventually killed it. By then, its damage was estimated at US$4 billion, and the North Koreans made a profit of US$80,000.
The No More Ransom initiative was launched in 2016, but the criminals continued to rake in their millions with new iterations of ransomware. It’s estimated that between April 2020 and August 2022, in the US alone, 1500 attacks on healthcare companies involved some 100 million files, with a third of cases resulting in a ransom payment.
Well-publicised attacks on Colonial Pipeline, Solar Winds and Kaseya helped turn the tide. These were critical infrastructure, and even non-affected companies saw advantages in cooperative responses backed by credible law enforcement. The Russian Government also collaborated, shutting down gangs such as REvil and Conti that had brought too much heat from Western agencies.
The FBI penetrated the biggest ransomware gang, LockBit, which had carried out 2500 successful attacks and netted US$500m. Its mastermind was Dmitry Khoroshev, who was based in Voronezh in southwest Russia. He was exposed by Operation Cronos, whose ‘naming and shaming’ campaign effectively ended his career.
The cybercriminals are far from defeated, having clocked up some 4900 attacks in the US between 2021 and 2024, with ransoms totalling US$3.1b. Shortland says the means to combat this already exist: “… we can make ransomware more difficult to carry out and less profitable at every stage of the attack life cycle: the development of the malware and attack infrastructure, the recruitment of affiliates, accessing victims’ networks, data exfiltration, encryption, extortion, and ransom payment”.
Again, Shortland makes a comparison with an epidemic, although this has moved on from Aids/HIV. Ransomware is not something that can be ‘beat’, she says. “As with Covid-19, there are precautions we can take to avoid becoming a victim, measures that will help us cope, and methods to prevent infection from spreading.”
We Know You Can Pay a Million: Inside the Dark Economy of Hacking and Ransomware, by Aja Shortland (Profile Books).
Nevil Gibson is a former NBR editor-at-large.
This content was supplied free to NBR.
Sign up to get the latest stories and insights delivered to your inbox – free, every day.